There are two options for Active Directory Identity Sources with PSC (SSO) 6.0:
- Active Directory (Integrated Windows Authentication)
- Active Directory as an LDAP server
Note: there are underlying issues using ‘AD Integrated Windows Authentication’ when VMware SRM is part of a solution.
The chosen SSO identity source outlined in this example is ‘Active Directory as an LDAP Server’. This is also the identity source configuration used for an EHC solution.
The following steps detail how to add AD LDAP authentication in vCenter 6.0 (PSC):
1. Browse to https://vcenter FQDN:9443 and login to the web client as the SSO administrator: administrator@vsphere.local.

2. Navigate to Administration->Single-sign-on->Configuration, then click the ‘Identity Sources’ tab.
3. Click the green + to add a new identity source.
4. Select Active Directory as an LDAP server and fill in the details. The following images provide an example configuration:


5. Click on the ‘Test Connection’ button in order to validate AD connectivity is successful.
Now that the AD identity source is configured and AD connectivity has been validated you can proceed to add AD user(s) to the SSO administrators group.
Note: Adding Groups is not supported – Assign only individual users from your Active Directory to the vCenter Single Sign-On Administrators group. Please refer to the following VMware KB:
https://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2095342
Assigning AD User to the vCenter Single Sign-On Administrators group:
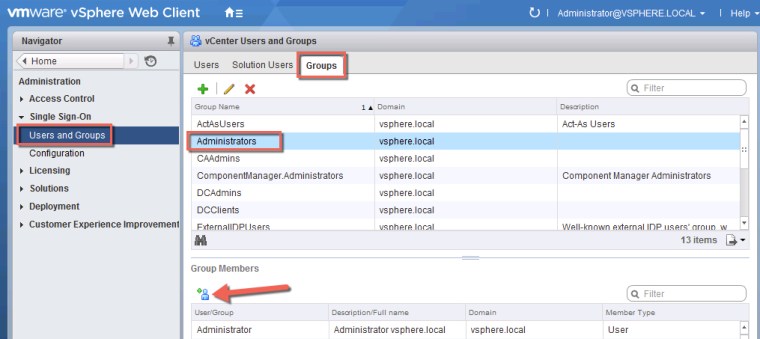
1. Under SSO select ‘Users and Groups’
2. Select the ‘Groups’ tab and chose ‘Administrators’ from the list provided. Under ‘Group Members’ click the green + member icon:
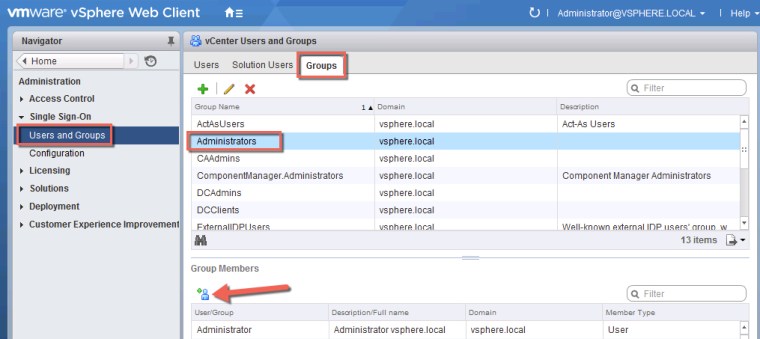
3. Select your domain and add your desired users to the SSO Administrators group:

Default EHC vCenter SSO administrators: app_nsx_sso, app_vro_sso, ehc_sysadmin
Assigning vCenter Server Roles
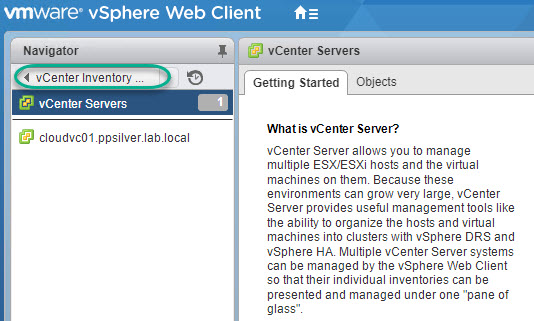
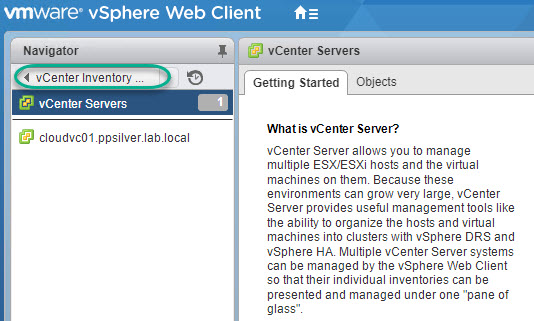
From the web client Click on ‘Home’, ‘vCenter Inventory Lists’, ‘vCenter Severs’:
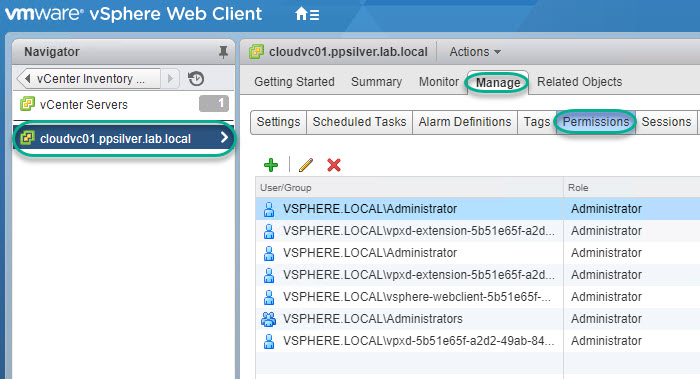
Click on your desired vCenter server, ‘Manage’ and chose ‘permissions’ and click the green + to add and assign roles:
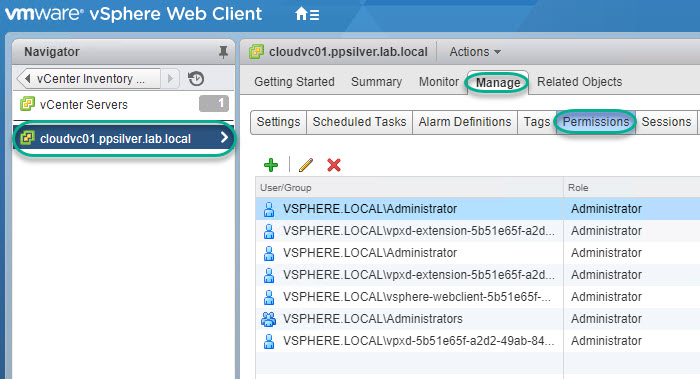
In the case of EHC the following roles apply:
– Add the DOMAIN\VC_Admins and assign the group the Administrator role.
– Add the DOMAIN\VC_App_Logins_RW and assign the group the
Administrator role.
– Add the DOMAIN\VC_ReadOnly and assign the group the Read Only role.
– Add the DOMAIN\VC_App_Logins_RO and assign the group the Read Only
role.












Do you have any recommendations on using LDAP on 389 vs the LDAP global catalog on 3268?
Hi Brian,
Primary domain controller LDAP server for the domain.
Use the format ldap://hostname:port or ldaps://hostname:port. The port is typically 389 for ldap: connections and 636 for ldaps: connections. For Active Directory multi-domain controller deployments, the port is typically 3268 for ldap: connections and 3269 for ldaps: connections.
Reference:
http://pubs.vmware.com/vsphere-60/index.jsp?topic=%2Fcom.vmware.vsphere.security.doc%2FGUID-98B36135-CDC1-435C-8F27-5E0D0187FF7E.html&resultof=%22%33%32%36%38%22%20